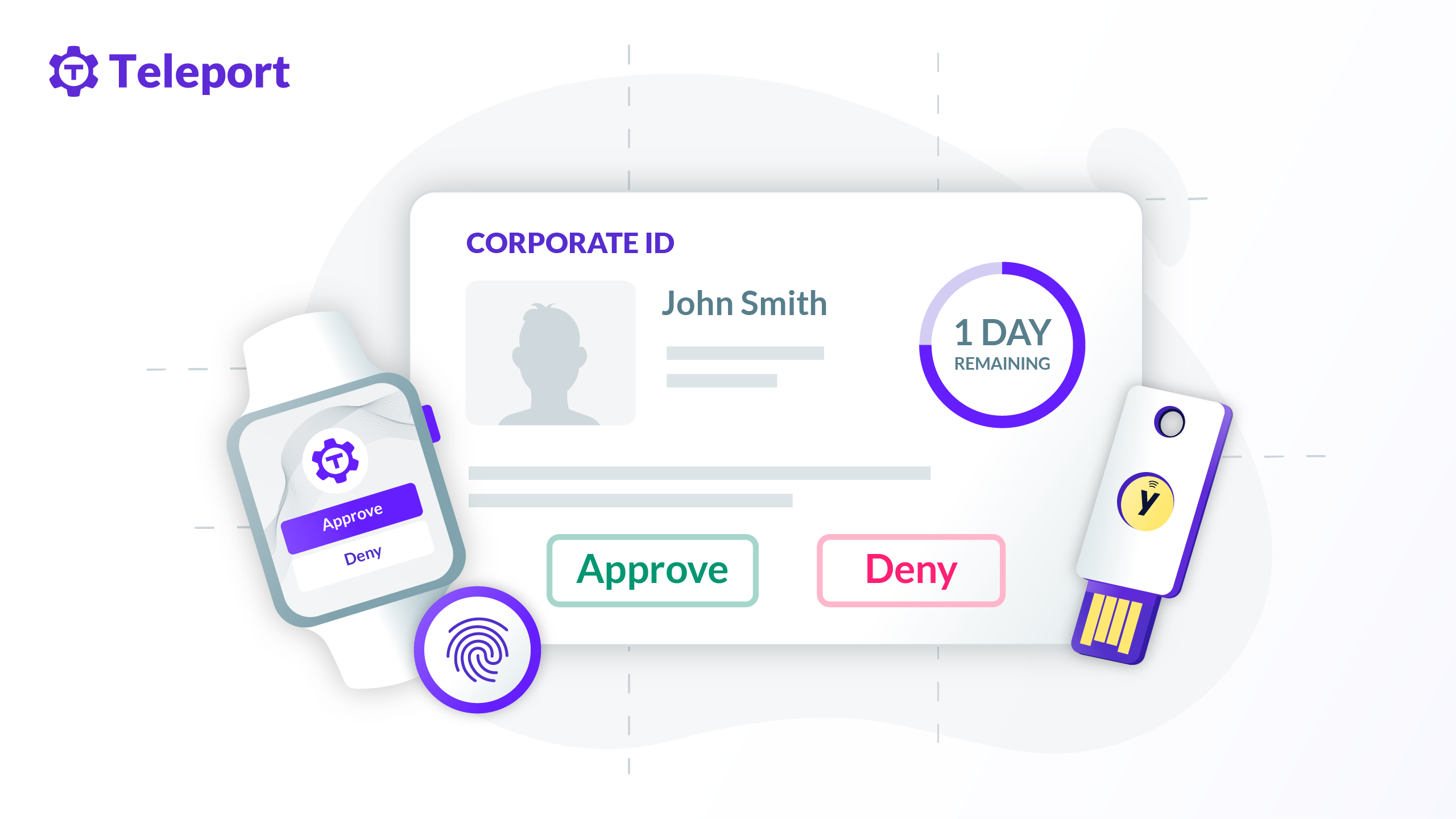
Authentification Guide — Two authenticators
5 ways attackers can bypass two-factor authentication - Hoxhunt
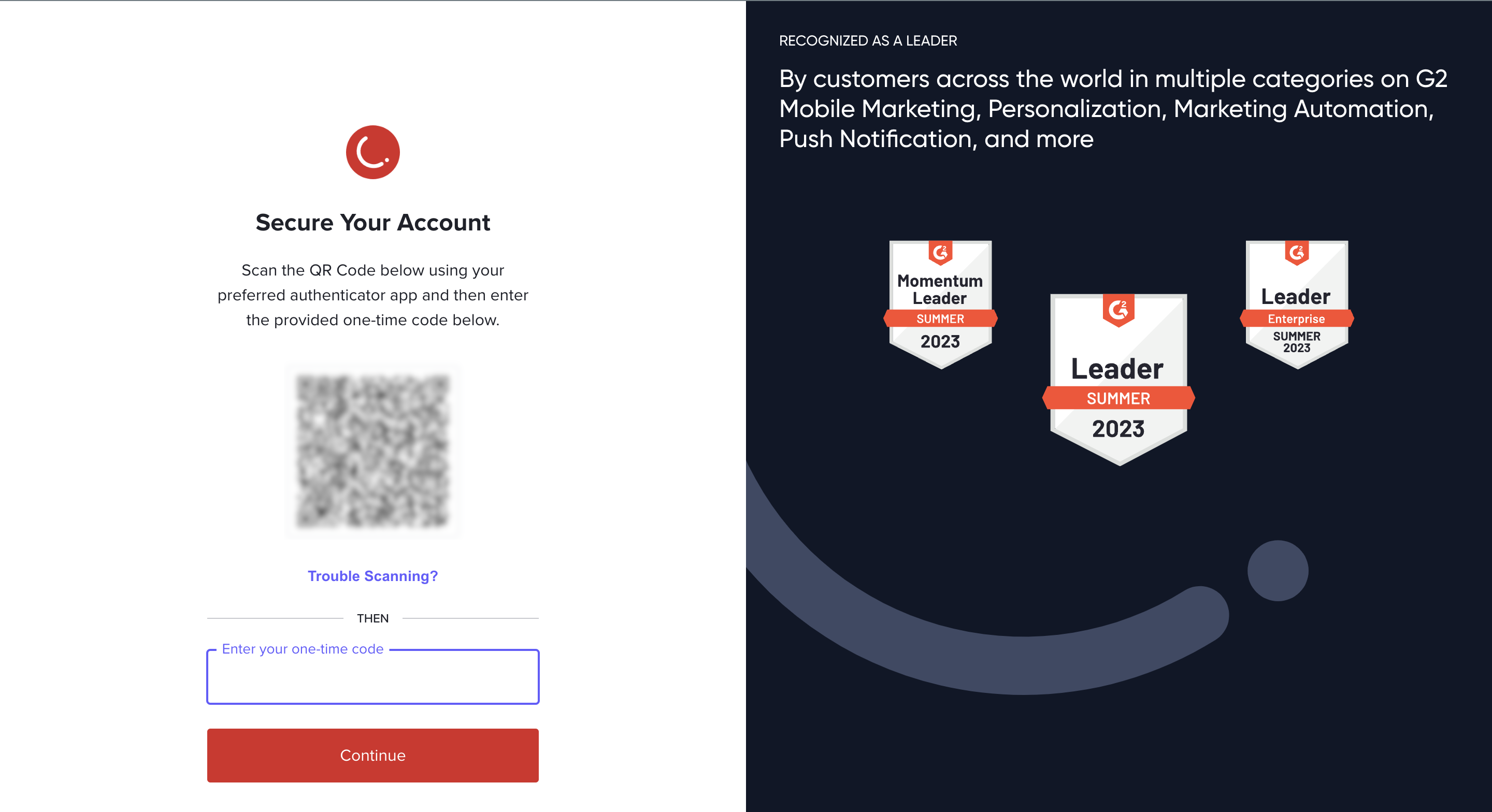
Tutorial: SSH 2fa using Using Google Authenticator

Two-factor authentication explained: How to choose the right level
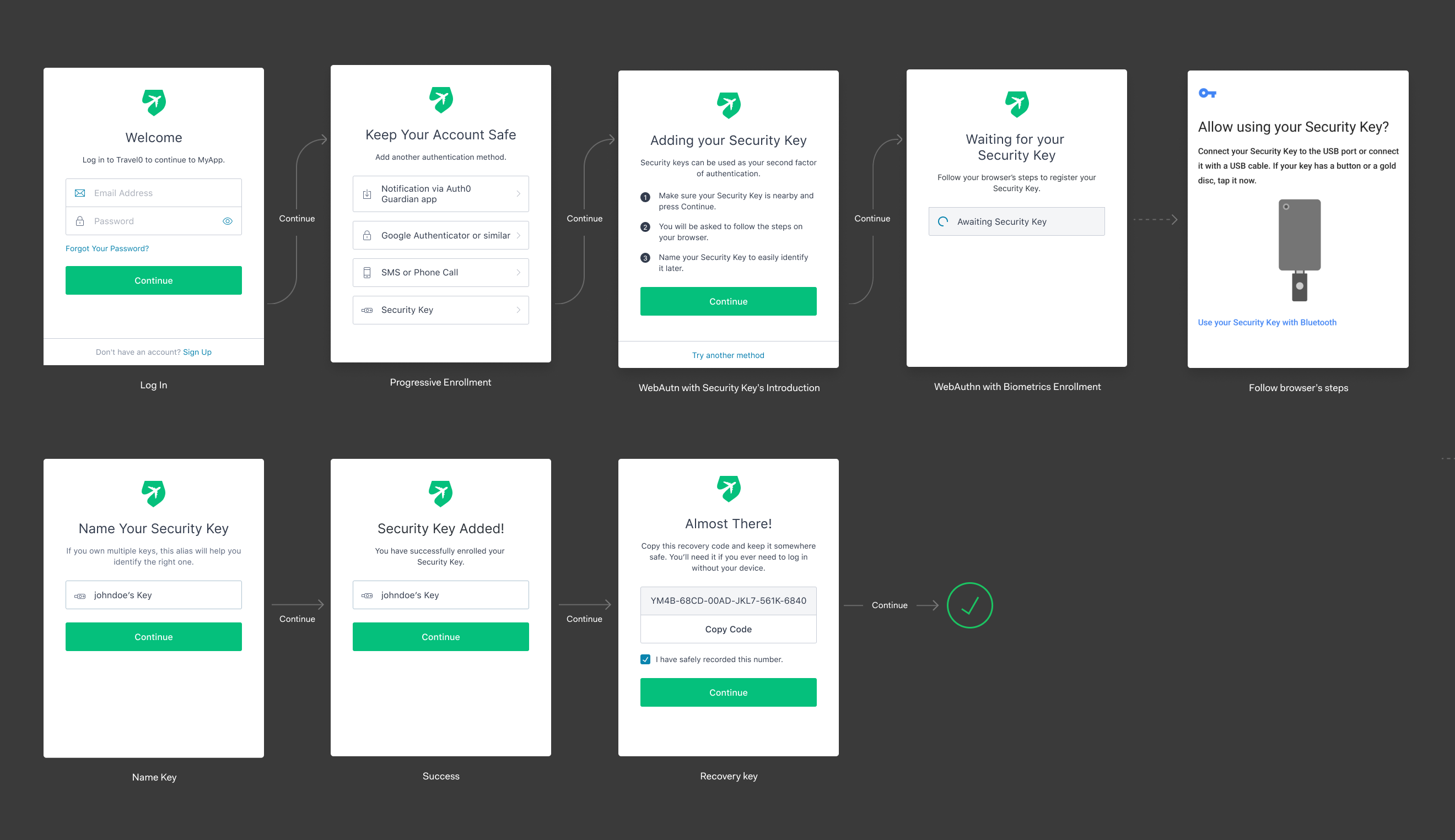
FIDO Authentication with WebAuthn

Two-Factor Authentication HackerOne Platform Documentation

Two Factor Authentication Explained: Cracking the Code

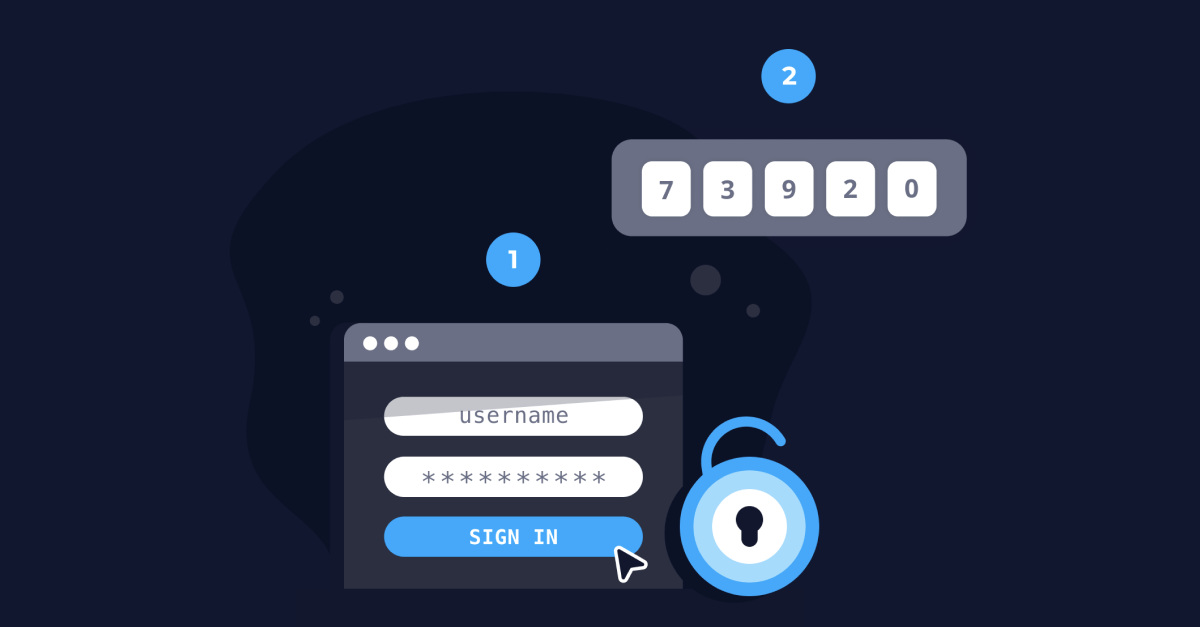
How Does Two-Factor Authentication (2FA) Work? - Merchant Fraud

Two-Factor Authentication: A Security System for Your Digital Life
No, You Shouldn't Turn Off Two-Factor Authentication
Two-Factor Authentication (2FA)

What is Two-Factor Authentication (2FA)? and Why you need one?

Twilio Account Login Change: Mandatory Two-Factor Authentication

Two Factor Authentication
:max_bytes(150000):strip_icc()/twofactor-authentication-2fa.asp-final-5dc205d2a08b447abfb2e15eb131e28e.png)
What Is Two-Factor Authentication (2FA)? How It Works and Example
Authentification Guide — Two authenticators
- Best Price $ 12.50. Good quality and value when compared to berghoff.ir similar items.
- Seller - 601+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Twist Pink Epi Rose Ballerine Leather Chain Wallet Bag
Buy It Now 12d 10h -

Sac de voyage pegase en toile Louis Vuitton Brown in Leather - 33772517
Buy It Now 8d 14h -

Authentic Vintage 90s Louis Vuitton Luggage Bag
Buy It Now 4d 12h -

Gucci, Bags
Buy It Now 28d 7h -
Louis Vuitton vintage porte-documents (BT 0870) - Auction FINE
Buy It Now 23d 9h -

New York City, USA - May 2, 2016: Emma Stone attends the 2016 Met Gala Stock Photo - Alamy
Buy It Now 22d 16h -

Louis Vuitton Discovery Bumbag (Brown) – Luxxe
Buy It Now 8d 6h -

Louis Vuitton Yoga Mat Price: People not happy with Louis Vuitton's $2,390 yoga mat made of leather - The Economic Times
Buy It Now 13d 6h -

1,221 Polo G Photos & High Res Pictures - Getty Images
Buy It Now 22d 9h -

LOUIS VUITTON Reverse Monogram Loop Hobo 1267549
Buy It Now 4d 11h -

Chunky Razor Blade Necklace Chunky Chain Choker Thick Chain
Buy It Now 19d 19h -

PRADA RAFFIA EMBROIDERED LOGO TOTE BAG NATURALE - CRTBLNCHSHP
Buy It Now 9d 7h -

Louis Vuitton, Jewelry
Buy It Now 28d 5h -

Louis Vuitton Bordeaux Exotique Monogram Limited Edition Majestueux PM Bag Louis Vuitton
Buy It Now 11d 13h -

Louis Vuitton Pochette Metis - Monogram Vs. Empreinte (Comparison and Review)
Buy It Now 25d 6h -

Louis Vuitton Pre-owned Monogram Eclipse District PM Messenger Bag - Black
Buy It Now 6d 8h -

Bally Quilted Double Flap Bag, Luxury, Bags & Wallets on Carousell
Buy It Now 4d 19h -

Louis Vuitton Trainer Sneaker Boot 508 Purple Virgil Abloh Size LV 6
Buy It Now 28d 9h -

The Most Sought After Birkin: The Birkin 25
Buy It Now 12d 16h -

Hermes sales beat expectations, defying luxury sector gloom
Buy It Now 16d 12h -

Hermes Birkin Handbag Cuivre Togo with Palladium Hardware 40 at 1stDibs
Buy It Now 14d 9h -

Metallic Silver Lightweight Faux Leather - Lame & Metallic - Other Fabrics - Fashion Fabrics
Buy It Now 20d 6h -

Bag Organizer for Louis Vuitton Neverfull PM (Fixed Zipper Top
Buy It Now 11d 6h -

Sudadera de algodón bordada - Prêt-à-Porter 1ABYJT
Buy It Now 15d 16h